
DeTaSECURE - Creating Buzz with its Web 3 Cyber Security Solutions
Blockchain technology is known for its globally consistent ledger that does not depend on any centralized authority. Any change in the ledger must be approved by a majority of the decentralized network nodes under a consensus protocol and it protects the integrity of the transactions. This is the reason blockchain is ‘trustable’ by its design and the trust has really opened up a plethora of opportunities in this digital era. But is the blockchain ecosystem trustworthy enough? The ledger implementation may have flaws or even the implementation of cryptographic software libraries may be error-prone in a blockchain. We have also witnessed a rare 51% attack on blockchains like Bitcoin Gold, Ethereum Classic etc. in the past that resulted in significant double-spending. Popular chains like Bitcoin or Ethereum have obviously resisted such issues and found acceptance among the crypto community but there are huge challenges with smart contracts. DeTaSECURE is a new cybersecurity firm that is trying to address various issues regarding smart contracts and Web 3.

DeFi or decentralised finance has made it possible to trade various assets over blockchain without the intervention of a third party. The smart contracts act as financial robots and automate all processes like trading, lending, borrowing etc. The permissionless nature of DeFi has attracted a lot of investors into it and the TVL (Total Value Locked) has skyrocketed since its inception. DeFi comes with high rewards, but it also exposes investors to high risks. Anybody can write smart contracts and launch a DAPP (decentralized application). The majority of popular DeFi protocols are open source, so forks keep on coming into the market. But flaws are common in the codes and unscrupulous actors can exploit the flaws. So, billions of dollars locked in the DeFi Protocols draw great attention from malicious parties. The hackers really get enough time to analyze vulnerabilities in a particular protocol and plan an attack. Several applications or protocols have been targets of significant hacks in the past, resulting in the loss of a terrible amount of digital assets.
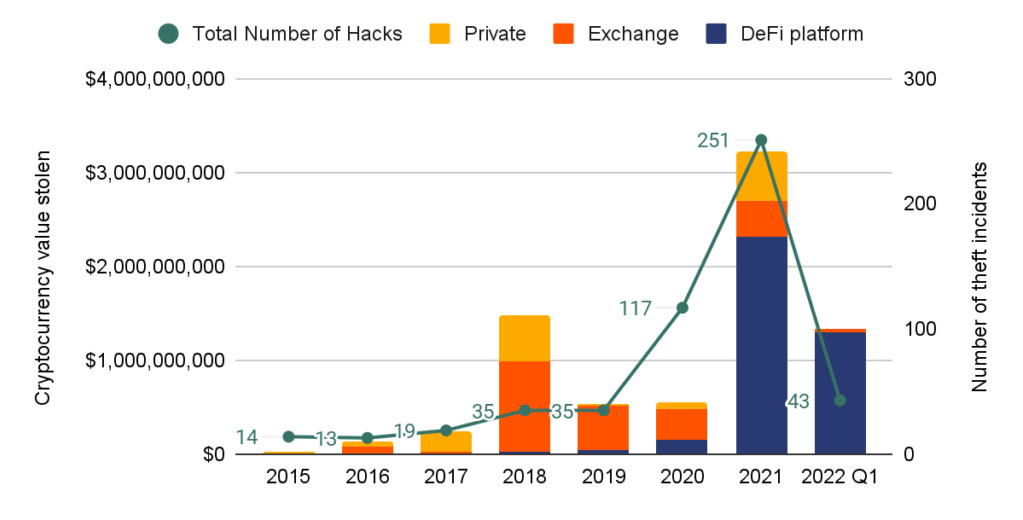
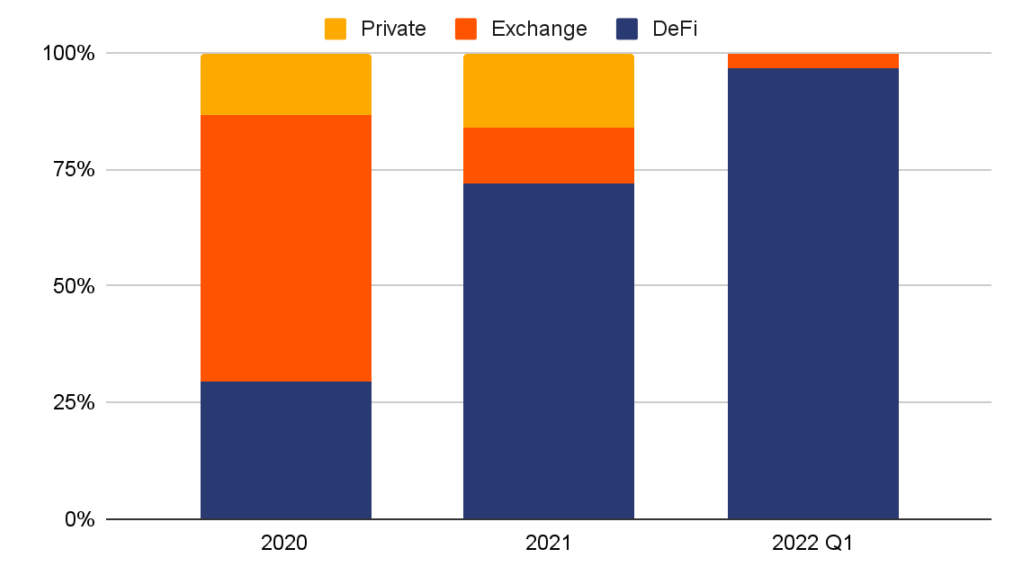
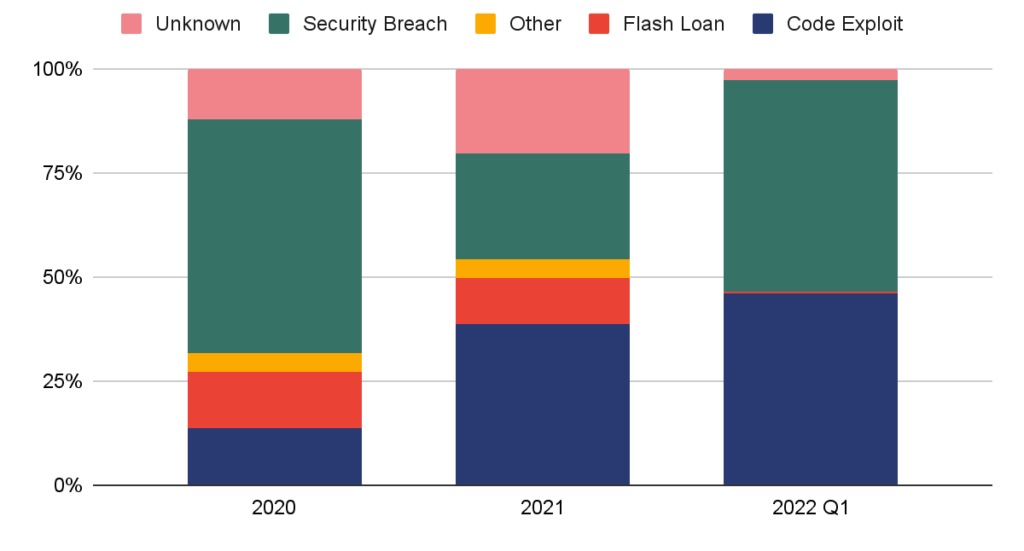
Approximately $3.2 billion worth of cryptocurrency was stolen by digital thieves in 2021 and 72% ($2.2 billion) of that was drained from DeFi protocols as per Chainalysis. The stealing from DeFi applications rose a mammoth 1330% in 2021 with respect to 2020. The hackers are having a dream run in 2022 also. In the first quarter of 2022 only, almost $1.3 billion-dollar worth of assets was stolen from all crypto-related platforms and DeFi contribution was astoundingly high. Almost 97% of the value stolen in the first quarter of 2022 was from DeFi platforms. In October alone, more than $718 million was stolen from DeFi platforms. At this rate, 2022 is going to be the biggest year for hacking. The most common method to attack the DeFi protocol is flash loans. A flash loan attack abuses smart contract security by borrowing uncollateralized funds from lending protocol and manipulating the price of a given asset, driving up its value. Recently, cross-chain bridges have become popular as they allow users to transfer cryptocurrency between different chains. But such bridges are vulnerable due to code errors or operational flaws. Ronin bridge hack this year resulted in over $600 million loss and it happened as the hackers could obtain several validator keys.
2022 has been a tumultuous year in cryptocurrency and the market is quite bearish. But a bear market can’t wipe out the bull market adoption. Global adoption is growing significantly and there is an inflow of capital from fresh investors. This is also allowing the ecosystem to grow continuously without the absence of upside price movement. Europe and the United States remain steady in the DeFi adoption due to regulatory clarity but people from emerging economies are displaying a high turnaround in the adoption curve and it is most probably due to the fact that they can derive better extractable value from cryptocurrency due to the unstable economic situation. Ethereum paved the way for DeFi but the high cost of transactions created an entry barrier for retail investors. Many EVM-enabled competitor blockchains have arrived in the market now and the Layer 2 ecosystem of Ethereum has also expanded. Retail investors can access DeFi protocols on several chains with a nominal transaction fee. Numerous new protocols are being launched every day to capture this opportunity, but the security issue still remains unsolved. Even the old popular protocols keep on getting hacked. A DeFi lending protocol like bZx, launched in 2019, has been hacked 4 times since its launch and the last hack happened in November 2021. There is no doubt that all DeFi applications should be properly audited, and all API connections also should be assessed for vulnerabilities. Astonishingly, hackers are breaching the security of numerous audited protocols also. This raises a lot of questions regarding the quality and method of the audit.
A DAPP must be zero-day vulnerable to protect the consumers. Existing audit infrastructure has simply failed to provide that. Here comes the role of DeTaSECURE. Their team comprises esteemed cyber security experts with experience in top global enterprises. It is a young organization and started operations during the pandemic with a small team. Now they have 40+ B2B customers that include both startups and Fortune 500 companies across 15+ countries. DeTaSECURE’s most popular product is GETSecured. This is a proprietary comprehensive security scanning tool that identifies breached data instances and web application vulnerabilities. DeTaSECURE wants to focus heavily on Web 3 nowadays. They won the ‘ETHNYC’, ‘Polygon BUIDL’ and Solana Hackathon’ by developing a fully automated smart contract scanner. This scanner can be used on or off-chain and uses AI (Artificial Intelligence) to find erroneous codes or flaws. It can protect a DAPP to be deployed on the testnet or mainnet if a vulnerability is detected. The scanner also generates a detailed report that helps to identify exact bugs in the codes. DeTaSECURE is already getting good attention from Web 3 companies for its services like contract audit, threat modelling, security architecture review, breach monitoring and VA/PT program to prepare for any attacks. The firm also offers security training and education programs for its clients.
The Internet has continuously evolved since its inception. Web 2, the internet we know, is dominated by centralized corporations. Now, we are at the beginning of Web 3, which has a vision of distributed ownership and control, but the path is challenging. Current Web 3 applications are being run using legacy infrastructures only. To fulfil the true vision of Web 3, all components of online services should be decentralized or distributed. Obviously, it is not going to happen very soon. Web 3 in its present form inherits a lot of security vulnerabilities of the second generation of the web. Here, DeTaSecure’s service becomes instrumental. As they have rich experience in handling Web 2 companies, they are very equipped to handle the issues in the Web 2 to Web 3 transition. A DAPP’s security is not only related to the smart contract codes but also to the front end and other parameters. Curve Finance faced a massive attack on 9th August 2022. No, it was not a smart contract exploit. The attackers conducted a DNS Poisoning attack. During the attack period, users were redirected to a fake website whenever they tried to access the original website. The attackers became able to steal $575K worth of crypto assets from the users of Curve this way. Transition to Web 3 really has serious implications for the digital transformation of fintech, commerce and many other processes. The emphasis on security will be the primary ingredient for the long-term success and adoption of Web 3. DeTaSECURE is getting ready to play a key role in this with its comprehensive security solution and services that take care of everything to improve the overall security posture of Web 3.
Follow DeTaSECURE on Twitter and LinkedIn for more updates and recent facts. It will help you to learn more about good security practices and how to maintain cyber hygiene in your organization. Here is the link to book a free consultation.
This article was first published here.
Follow Me
👉 Twitter @paragism_

